Hackers are always finding new ways to break into your devices. A troubling new vulnerability in iOS now allows hackers to spy on you through your keyboard.
Certo Software released a report revealing how cybercriminals are avoiding Apple’s stringent security measures to steal your information.
Essentially what hackers are doing is installing a third-party keyboard that features a keylogger into your iPhone.
They will disguise that keylogger in a small app and use Apple’s TestFlight tool for app developers to bypass Apple’s security checks. Hackers are hoping you download those apps and turn over your own information.
What is TestFlight?
Developers need a place to test their apps, and TestFlight provides a space for that. It lets developers upload unfinished versions of apps and send out links to testers. They have a range of testing options, too. Developers can have testers tinker with the whole app or create “App Clips” or specific test features. Testers have the option to test the whole app or “App Clips” and provide feedback to both the developer and Apple.
TestFlight app. (Apple )
It’s Apple’s top developer tool. Many of the reviews cite how easy it is to use and how it makes beta testing a breeze. There are some security concerns, however. Apple shares your name and email if you use the app. If you’re a tester, it shares the type of device you’re using, carrier and other information.
MORE: BEWARE OF FAKE BROWSER UPDATES ON YOUR MAC
How are hackers using TestFlight to steal your information?
Certo notes that hackers use a fairly straightforward practice. They will install a small app containing a custom keyboard. That keyboard features a keylogger, which records everything you type and transmits it to them. Once the app is installed on your phone, they will install the custom keyboard on your iPhone through your settings app and give the keyboard full access.
They will then switch your keyboard from the default one to their malicious version. It’s important to note that, oftentimes, these keyboards will look virtually identical to the iPhone’s default keyboard — which makes it nearly impossible to tell if you’re using a compromised keyboard.

A person holding a cellphone showing their apps. (Kurt “CyberGuy” Knutsson)
MORE: HOW TO PROTECT YOUR IPHONE FROM CYBERATTACKS WITH LOCKDOWN MODE
How you can protect yourself
To make sure you’re not using a compromised keyboard, you should check your keyboard settings in iOS. Here’s how you can check:
- Head to your Settings app
- Click General
- Select Keyboard
- Then click Keyboards
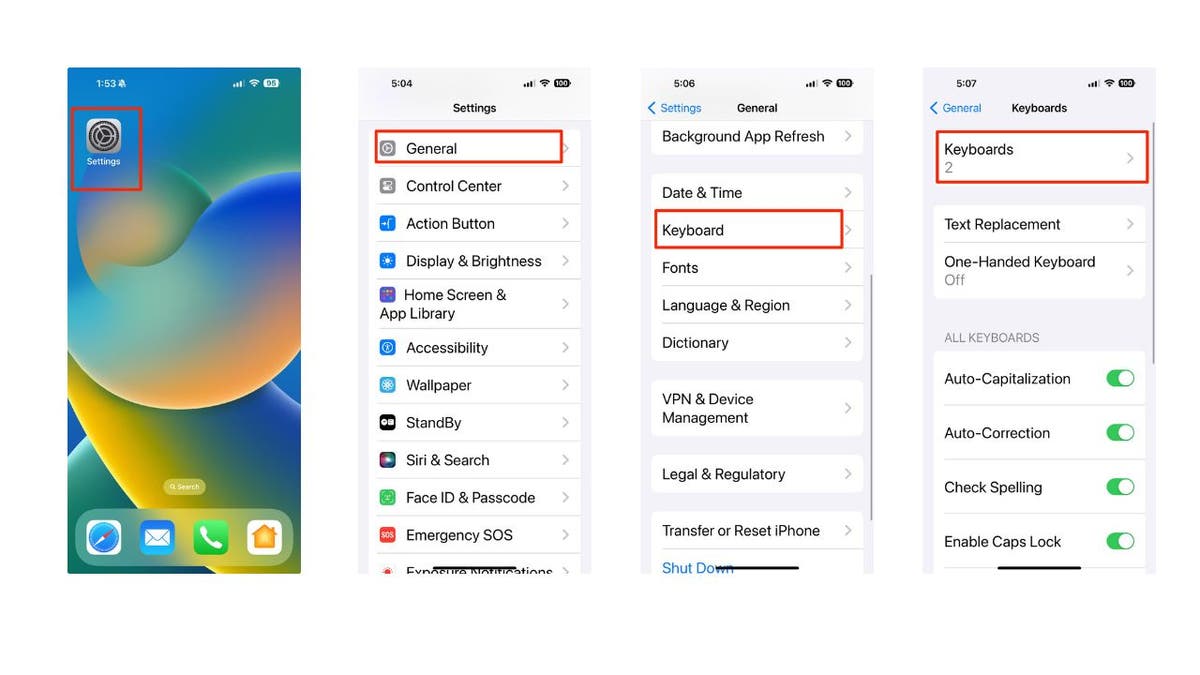
Steps to check your keyboard settings in iOS. (Kurt “CyberGuy” Knutsson )
- You should see which keyboards you’re using
- Click on Edit to delete any
- To delete a keyboard, just click on the red minus sign in front of the keyboard
FROM DATING SITES TO PHISHING EMAILS: HOW AI IS CREATING MORE REALISTIC SCAMS

Steps to check your iPhone keyboard settings in iOS. (Kurt “CyberGuy” Knutsson)
MORE: POLICE URGE PARENTS TO TURN OFF APPLE IPHONE SETTING DANGEROUS TO KIDS
How to protect your iPhone from keyboard spying attacks
Avoid downloading apps from unknown or untrusted sources. Only download apps from the official App Store or from reputable developers.
Be careful when using TestFlight to test apps. Read the app description and reviews carefully before installing. Do not grant full access to any custom keyboards that you do not recognize or trust.
Check your keyboard settings regularly and delete any suspicious or unwanted keyboards. You can follow the steps we outline above to do this.
Update your iOS to the latest version and install any security patches that Apple releases. This can help fix any vulnerabilities or bugs that hackers might exploit.
Have good antivirus software on all your devices. Keeping hackers out of your devices can be prevented if you have good antivirus software installed. Having antivirus software on your devices will make sure you are stopped from clicking on any potential malicious links that may install malware on your devices, allowing hackers to gain access to your personal information.
Find my review of Best Antivirus Protection here.
What should you do if you are a victim of a keyboard spying attack
If it has already happened, then you should take immediate action to minimize the damage and secure your device. Here are some steps that you can follow:
APPLE RELEASES URGENT IOS UPDATE DUE TO SECURITY EXPLOITS
1. Change your passwords. If hackers have recorded your passwords using the keylogger, they could access your online accounts and steal your data or money. ON ANOTHER DEVICE (i.e. your laptop or desktop), you should change your passwords for all your important accounts, such as email, banking, social media, etc. You want to do this on another device so the hacker isn’t recording you setting up your new password on your hacked device. Use strong and unique passwords that are hard to guess or crack. You can also use a password manager to generate and store your passwords securely.
2. Monitor your accounts and transactions. You should check your online accounts and transactions regularly for any suspicious or unauthorized activity. If you notice anything unusual, report it to the service provider or the authorities as soon as possible. You should also review your credit reports and scores to see if there are any signs of identity theft or fraud.
3. Contact your bank and credit card companies. If hackers have obtained your bank or credit card information, they could use it to make purchases or withdrawals without your consent. You should contact your bank and credit card companies and inform them of the situation. They can help you freeze or cancel your cards, dispute any fraudulent charges and issue new cards for you.
4. Alert your contacts. If hackers have accessed your email or social media accounts, they could use them to send spam or phishing messages to your contacts. They could also impersonate you and ask for money or personal information. You should alert your contacts and warn them not to open or respond to any messages from you that seem suspicious or unusual.
5. Restore your device to factory settings. If you want to make sure that your device is completely free of any malware or spyware, you can restore it to factory settings. This will erase all your data and settings and reinstall the original iOS version. You should back up your important data before doing this, and only restore it from a trusted source.
6. Use identity theft protection: If hackers were to record everything you type on your keyboard, they could use this information to open accounts in your name, access your bank and credit card accounts, and impersonate you online. That’s where identity theft protection companies come in. They can monitor personal information like your home title, Social Security Number (SSN), phone number and email address and alert you if it is being used to open an account. They can also assist you in freezing your bank and credit card accounts to prevent further unauthorized use by criminals. See my tips and best picks on how to protect yourself from identity theft.
Kurt’s key takeaways
There are hundreds, if not thousands, of ways hackers can steal your information. You can do yourself a favor by giving them one less avenue to hack you by being careful about where you download your apps and keeping an eye out for malicious software.
CLICK HERE TO GET THE FOX NEWS APP
Do you think tech companies like Apple should take additional measures to protect you from potential security breaches, or do you believe it’s primarily your responsibility to safeguard your devices? Let us know by writing us at Cyberguy.com/Contact
For more of my tech tips & security alerts, subscribe to my free CyberGuy Report Newsletter by heading to Cyberguy.com/Newsletter
Ask Kurt a question or let us know what stories you’d like us to cover.
Answers to the most asked CyberGuy questions:
CyberGuy Best Holiday Gift Guide
Copyright 2023 CyberGuy.com. All rights reserved.
By
Source link



